You know that little padlock icon in your browser’s address bar? The one that makes you feel safe when you’re checking your bank account or sending a private message? Well, that security—the very foundation of trust on the internet—is facing a future threat so profound it’s forcing a complete rebuild. The threat comes from quantum computers. And the solution has a name: post-quantum cryptography, or PQC for short.
Now, don’t panic. The quantum apocalypse isn’t here yet. But the transition to quantum-resistant algorithms is a massive, slow-moving ship that needs to start turning now to avoid the iceberg. This isn’t just for spies and governments. It’s for your emails, your medical portals, your online shopping…honestly, for every single web app you use.
Why Today’s Web Security Has an Expiration Date
Let’s break it down simply. Most web security today relies on math problems that are incredibly hard for classical computers to solve. Problems like factoring huge numbers (RSA encryption) or finding discrete logarithms (ECC). They’re the digital equivalent of a lock that would take billions of years to pick.
Here’s the deal: quantum computers, using a principle called Shor’s algorithm, could solve these specific problems in hours or days. It’s like handing a master locksmith a futuristic key that reshapes itself to fit any pin-tumbler lock. Poof. The padlock opens.
The Looming “Harvest Now, Decrypt Later” Problem
This is the real kicker. Adversaries with foresight are likely already collecting and storing encrypted data today—sensitive government communications, intellectual property, health records—with the full intention of decrypting it once a powerful enough quantum computer exists. That data has a long shelf life. A secret stolen today could be exposed a decade from now. That thought should give anyone pause.
What Is Post-Quantum Cryptography, Really?
In a nutshell, PQC refers to cryptographic algorithms designed to be secure against attacks from both classical and quantum computers. They’re built on different, more complex mathematical foundations—lattices, codes, multivariate equations—that, as far as we know, even quantum algorithms find daunting.
Think of it like this: we’re not just making the existing lock stronger. We’re inventing a completely new type of lock, one that doesn’t even have keyholes in the traditional sense. The old lock-picking tools, quantum or not, just won’t work on it.
The NIST Standardization: A Major Milestone
After a six-year global competition, the U.S. National Institute of Standards and Technology (NIST) has selected the first group of PQC algorithms to standardize. This is a huge deal—it gives developers and companies a trusted, vetted blueprint to start building with. The frontrunner for general encryption (like that browser padlock) is called CRYSTALS-Kyber. For digital signatures, there’s CRYSTALS-Dilithium, among others.
How PQC Will Sneak Into Your Daily Web Experience
You won’t wake up one day and click a “quantum upgrade” button. The migration will be mostly invisible, happening in the background. But it will touch everything.
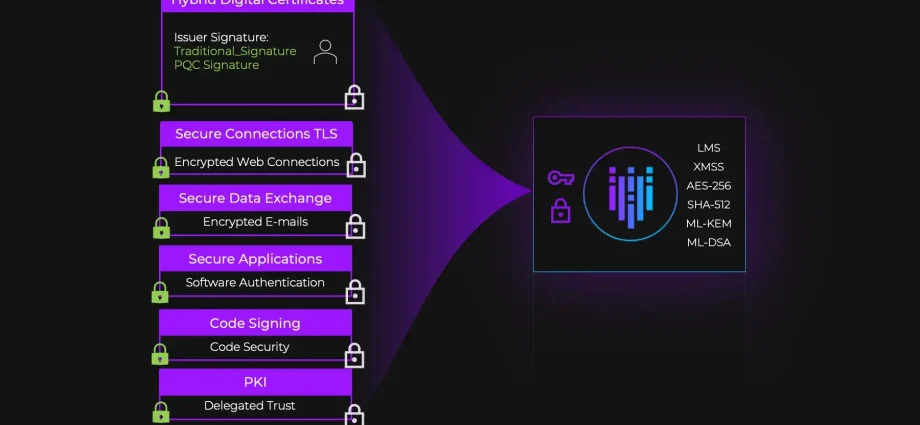
Here’s a quick look at some everyday applications and the changes PQC will bring:
| Web Application | Current Protection | Post-Quantum Change |
| Secure Websites (HTTPS) | RSA or ECC for key exchange | Hybrid models (Kyber + traditional) then full PQC |
| Private Messaging (Signal, WhatsApp) | ECC-based protocols | Updated protocols using PQC signatures & key encapsulation |
| Digital Signatures (DocuSign, Gov’t IDs) | ECDSA or RSA | Algorithms like Dilithium or Falcon |
| Software Updates | Code signed with RSA/ECDSA | PQC-signed updates to prevent malicious quantum-era spoofing |
| VPNs & Remote Access | Classical key exchange | Integration into protocols like IKEv2/IPsec |
The transition will likely use “hybrid” modes first. This means a connection will use both a traditional algorithm and a post-quantum one. It’s a safety belt—if the new PQC algorithm has an undiscovered flaw, the classical encryption is still there as a backup. Smart, right?
The Bumps on the Road to a Quantum-Safe Web
It’s not all smooth sailing. This upgrade comes with real, tangible costs and challenges for developers and companies—which ultimately affect how quickly it reaches you.
- Performance Hit: PQC algorithms are generally bigger and slower. Public keys and signatures can be significantly larger. This means slightly more data to transmit, a bit more memory to store, and a touch more CPU to process. For most everyday web apps, this will be negligible. But for huge, high-traffic systems or tiny IoT devices, it’s a genuine engineering puzzle.
- The Implementation Minefield: Rolling out new crypto is notoriously tricky. A tiny bug can create a giant vulnerability. The industry needs time to test, test, and test again in real-world environments. Rushing this would be, well, disastrous.
- The Legacy System Headache: Countless web applications run on old systems that are difficult to update. Getting PQC into every nook and cranny of the global internet infrastructure is a decade-long project, minimum.
What Can You Do? (Spoiler: It’s Not Nothing)
As an everyday user, you’re not expected to implement algorithms. But awareness creates demand. You can:
- Ask Questions: When using a sensitive web service, especially from your bank, healthcare provider, or password manager, ask if they have a post-quantum migration strategy. It shows you care about long-term security.
- Embrace Updates: Seriously. When your browser, phone, or apps prompt for an update, do it. These updates will increasingly contain the foundational PQC libraries needed for the transition.
- Think Long-Term for Your Data: If you have data that absolutely must remain secret for 10, 20, or 30 years, you need to consider its encryption today. This is a niche concern for most, but a critical one for some organizations.
Look, the move to post-quantum cryptography is perhaps the most unsexy, yet utterly vital, infrastructure project of the digital age. There’s no flashy UI, no viral feature. It’s the painstaking work of replacing the invisible pipes and wires that keep the internet’s house standing.
It reminds us that digital trust is not a static thing. It’s a continuous act of maintenance and foresight. The quantum threat is still over the horizon, but the time to build the seawall is while the sun is still shining. The quiet, ongoing work to bake PQC into everyday web applications is, in fact, a profound commitment to preserving our private digital futures.